Enhanced Security: Automating account creation and removal in real time reduces the risk of security breaches by ensuring that only authorized users have access to sensitive information.
What Is Identity and Access Management?
.png)
Identity Access Management
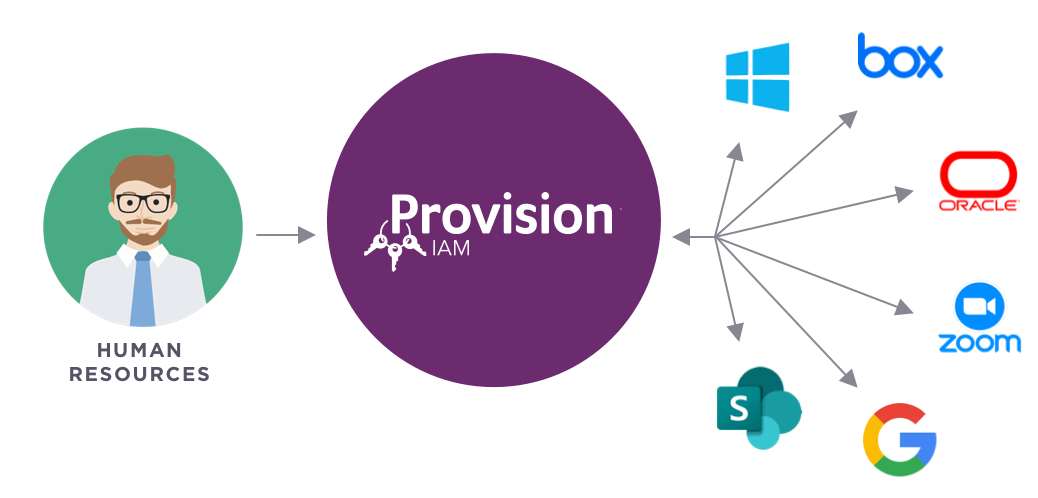
The concept of Identity and Access Management (IAM) might seem complicated at first, but once implemented, it can simplify many of your daily business operations. IAM is a framework for managing digital identities and controlling access to resources. It’s especially critical for modern banks and credit unions that handle vast amounts of sensitive information, from personal data to financial transactions.
This data is highly vulnerable to breaches and cyberattacks without a robust IAM system like Provision IAM.
.png?width=1452&height=1434&name=photos@2x%20(1).png)
How Does IAM Work?
Identity Access Management uses usernames, passwords, multifactor authentication, and biometrics identification to determine who has access to specific data and what they can do with it. IAM automates account provisioning, tracks user access and permissions across all of the systems your team uses on a daily basis, and enhances cybersecurity. It allows your HR and IT teams to spend less time preparing for internal and external audits, providing real-time documentation to auditors and increasing the efficiency of the audit process.
IAM Core Components
IAM consists of two core components: Identity Management and Access Management.
Identity Management involves creating and maintaining user identities and ensuring accurate lifecycle management from onboarding to deactivation:
- When a new employee joins, the bank sets up and verifies their credentials against existing records.
- The IAM system then assigns access rights based on the employee's role.
- As roles change, such as during departmental transfers, the system updates permissions accordingly.
- Access is promptly deactivated following an employee's departure or termination.
The IAM system monitors user activity to ensure compliance with banking regulations and detect unauthorized access. Multifactor authentication (MFA) enhances security by requiring multiple identity verification methods, like passwords and fingerprints.
Identity Management is vital for verifying user authenticity and maintaining up-to-date records.
Access Management, on the other hand, focuses on controlling user access to resources. It employs Role-Based Access Control (RBAC).
This part of the system ensures users have the appropriate level of access based on their roles or attributes, reducing the risk of unauthorized data access. For example, a bank employee working in customer service might only have access to customer profiles and transaction histories. In contrast, a financial analyst might access broader financial data and reporting tools.
The Benefits of IAM
There are many reasons an Identity and Access Management system should be an essential tool in your organization. An IAM system can provide:
Regulatory Compliance: An Identity and Access Management solution helps financial institutions meet industry-specific compliance requirements by tracking user access 24/7 and providing real-time, audit-ready documentation.
Streamlined Access Management: IAM gives organizations more control over access to confidential data, ensuring permissions are accurately managed and updated as needed.
Operational Efficiency: An Identity and Access Management solution reduces manual tasks for employees, allowing staff to focus on core business functions and increasing productivity.
Provision® Is the Identity and Access Management Solution Your Financial Institution Needs
Take your financial institution’s security and efficiency to the next level with Provision IAM, a cutting-edge Identity and Access Management platform. Experience enhanced security, streamlined compliance, and improved operational efficiency.
Discover how Provision IAM can elevate your business operations. Contact us for a detailed consultation and take the first step toward better user access management.
